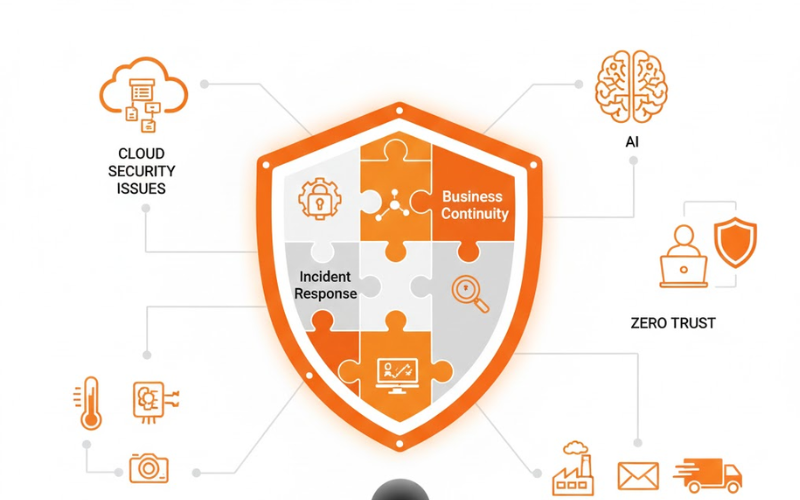
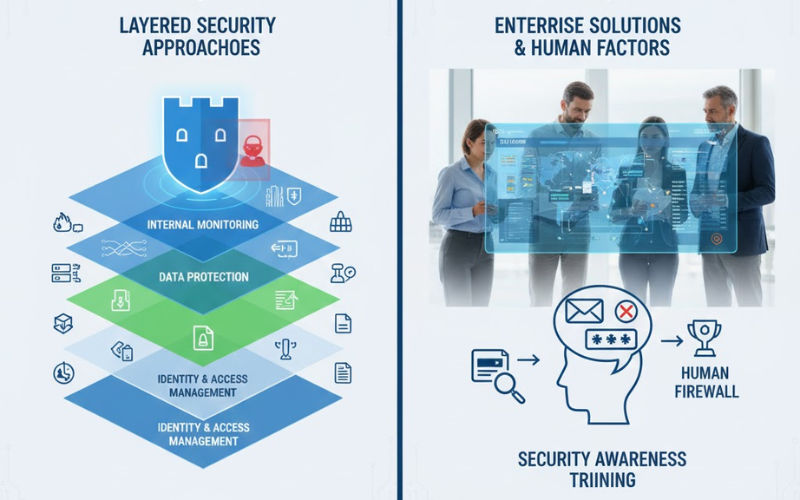
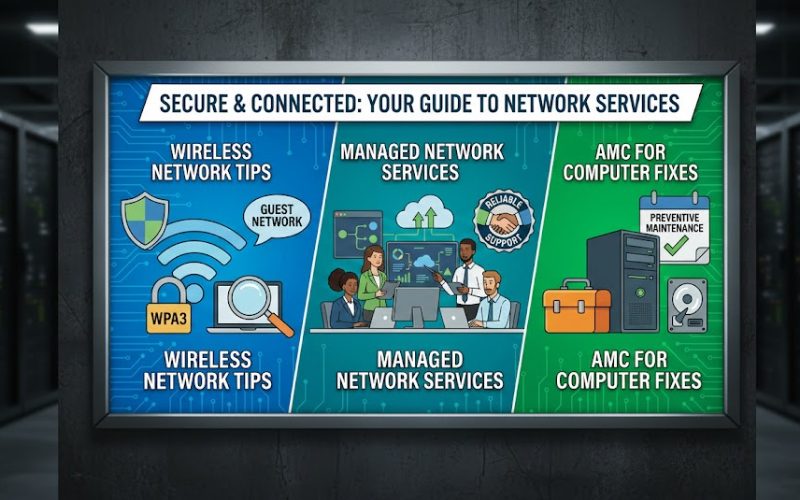
Securing the Digital Frontier: A Comprehensive Approach to Modern IT Security
The rapid shift to digital tools in nearly every field brings huge chances – but also serious risks. As companies rely more on tech systems to operate, safety isn’t just for IT teams anymore; it’s essential for survival. Staying aware and using strong safeguards helps defend critical data, keep clients confident, yet keeps operations running smoothly.