Our Blogs
As leaders in the IT supply sector for over five years, we are dedicated to offering the best service that guarantees your total satisfaction.
In the modern business environment, technology infrastructure is not a luxury — it is the backbone of every operation. Whether a company employs ten people or ten thousand, its ability to function efficiently, securely, and reliably depends almost entirely on the quality and coherence of its IT infrastructure. From the computers on every desk to the network cables running through the walls to the cameras watching over the premises, every component of a business's technology environment plays a critical role in its day-to-day performance and its long-term security.
In the modern business environment, technology infrastructure is not a luxury — it is the backbone of every operation. Whether a company employs ten people or ten thousand, its ability to function efficiently, securely, and reliably depends almost entirely on the quality and coherence of its IT infrastructure. From the computers on every desk to the network cables running through the walls to the cameras watching over the premises, every component of a business's technology environment plays a critical role in its day-to-day performance and its long-term security.
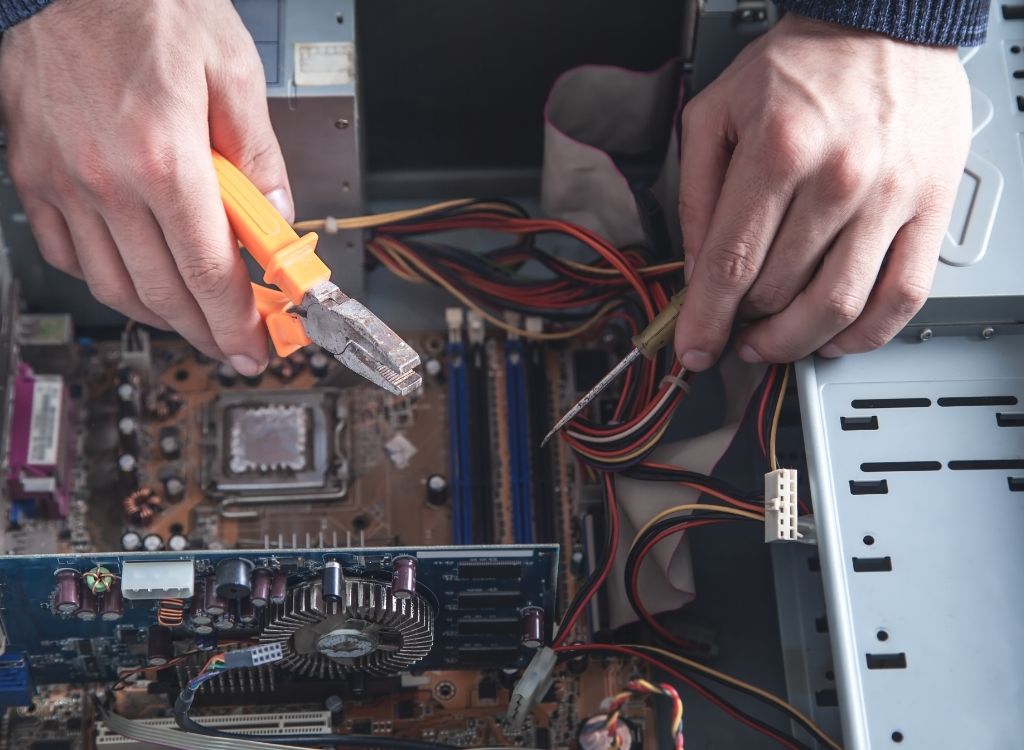
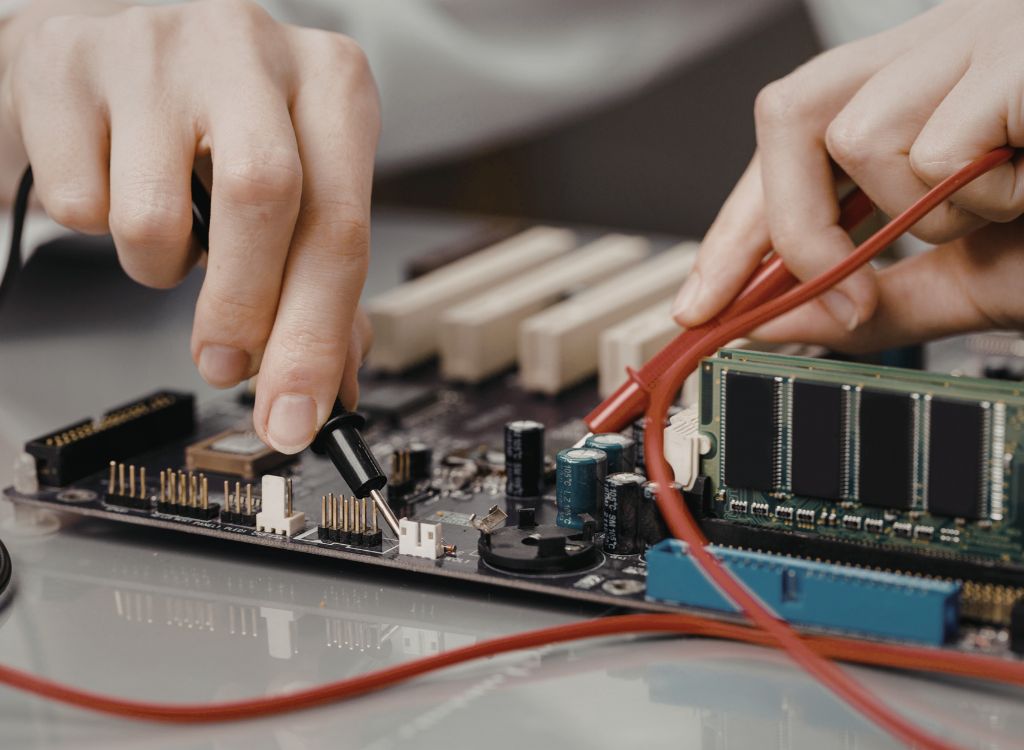
There is a pattern that plays out in businesses of every size, across every industry, with remarkable consistency. A computer starts running slowly. An employee mentions it once or twice. The issue gets deprioritized because there are more pressing things to deal with. Weeks pass. Then one morning, the system crashes during a critical task, taking hours of unsaved work with it. The hard drive fails. The data is gone. The repair bill is steep. The downtime costs even more.
There is a particular kind of quiet confidence that comes from knowing your home or business is being watched. Not in an unsettling way — but in the reassuring way that comes from having invested in a proper security infrastructure. A well-placed camera. A system that records reliably. Alerts that reach your phone before a situation escalates. That confidence is not accidental. It is the result of thoughtful planning and the right equipment.
There is a quiet revolution happening in the way Indians buy computers. Walk into any technology market in Bangalore, Chennai, Delhi, or Mumbai, and alongside the gleaming displays of branded laptops and pre-built desktop systems, there is a thriving ecosystem of assembled computers — machines built component by component, configured precisely to the buyer's needs, and priced with a transparency that branded alternatives simply cannot match. There is a quiet revolution happening in the way Indians buy computers. Walk into any technology market in Bangalore, Chennai, Delhi, or Mumbai, and alongside the gleaming displays of branded laptops and pre-built desktop systems, there is a thriving ecosystem of assembled computers — machines built component by component, configured precisely to the buyer's…
The laptop market has never offered more choice, more variety, or more confusion than it does today. Walk into any technology store or browse any major e-commerce platform and the sheer volume of options, ranging from budget devices priced under twenty thousand rupees to premium machines that cost several times more, can feel genuinely paralyzing. For professionals, creative practitioners, and business decision-makers trying to make an informed purchase, the central question inevitably becomes whether high-end laptops truly justify their premium pricing or whether mid-range alternatives can deliver comparable performance at a fraction of the cost.
There is a dangerous gap that exists in many organizations between the assumption of security and the reality of it. Systems are in place, passwords exist, an antivirus subscription is active, and the general feeling is that the bases are covered. This feeling — comfortable, reassuring, and completely at odds with the actual threat landscape — is one of the most exploited vulnerabilities in the entire field of cybersecurity.
There is a dangerous gap that exists in many organizations between the assumption of security and the reality of it. Systems are in place, passwords exist, an antivirus subscription is active, and the general feeling is that the bases are covered. This feeling — comfortable, reassuring, and completely at odds with the actual threat landscape — is one of the most exploited vulnerabilities in the entire field of cybersecurity.
There is a moment familiar to anyone who has ever sat in front of a sluggish computer trying to meet a deadline, render a file, or run a demanding application — the moment when the machine becomes the obstacle rather than the tool. It is the moment when the cost of not investing in the right technology becomes painfully, concretely clear. For professionals, businesses, and serious users who have reached that moment, the conversation inevitably turns toward high-end laptops and the broader ecosystem of technology solutions that support productive, secure, and efficient operations.
Every business has experienced it. A computer crashes on the morning of an important deadline. A laptop refuses to start during a critical client presentation. A network drive becomes inaccessible at exactly the moment someone needs the file it contains. These events feel like bad luck — isolated, unpredictable, unavoidable. In reality, the vast majority of them are the predictable consequence of a single, avoidable choice: waiting for something to break before doing anything about it.
Every business has experienced it. A computer crashes on the morning of an important deadline. A laptop refuses to start during a critical client presentation. A network drive becomes inaccessible at exactly the moment someone needs the file it contains. These events feel like bad luck — isolated, unpredictable, unavoidable. In reality, the vast majority of them are the predictable consequence of a single, avoidable choice: waiting for something to break before doing anything about it.
The conversation around IT security has for a long time been dominated by stories of large corporations, major data breaches, and sophisticated nation-state cyberattacks that make global headlines. This has created a dangerous misconception in the minds of many small and mid-sized business owners — the belief that cybercriminals are only interested in the big fish, and that operating a smaller business provides a kind of natural camouflage in the vast digital landscape. Nothing could be further from the truth.
The conversation around IT security has for a long time been dominated by stories of large corporations, major data breaches, and sophisticated nation-state cyberattacks that make global headlines. This has created a dangerous misconception in the minds of many small and mid-sized business owners — the belief that cybercriminals are only interested in the big fish, and that operating a smaller business provides a kind of natural camouflage in the vast digital landscape. Nothing could be further from the truth.
Security concerns have become increasingly prominent as property owners seek effective ways to protect their homes, businesses, and assets. The evolution of surveillance technology has made comprehensive security solutions more accessible and effective than ever before, with modern systems offering capabilities that were once available only to large organizations with substantial security budgets.
There is a particular kind of vulnerability that is unique to the digital age — the vulnerability of not knowing what you do not know. In the physical world, security risks are largely visible. You can see a broken lock, observe an unfamiliar person on your premises, or notice a missing piece of equipment.
The technology landscape continues evolving at breathtaking pace, creating challenges for businesses trying to maintain current, functional IT infrastructure. Traditional equipment ownership models that once seemed straightforward now present complications including rapid obsolescence, high upfront costs, maintenance burdens, and inflexibility. Alternative approaches like equipment rentals offer compelling advantages that address these challenges while providing additional benefits that ownership cannot match.
Smaller firms deal with distinct risks not always seen in bigger corporations. Limited funds make it hard to build full security systems or keep big defense squads on staff.
There is a moment that every business owner or IT manager dreads. It usually happens at the worst possible time — in the middle of a critical deadline, during a client presentation, or right before a major data backup was scheduled to run. A computer system fails. A laptop refuses to start. A server goes down. And suddenly, the entire rhythm of the business is disrupted while everyone scrambles to find a solution.
Successful CCTV systems require more than quality hardware; thoughtful design, proper installation, and ongoing maintenance all contribute to effectiveness. The design phase involves assessing security vulnerabilities, determining coverage requirements, and selecting appropriate equipment for specific applications. Professional security assessments can identify blind spots, optimal camera positions, and integration opportunities with existing security measures.
A single click can unravel months of work. When systems go down, confidence slips fast. Protection now sits at the heart of how groups operate online. Smaller teams face risks just like giants do. Because attacks shift constantly, defenses must too. Guarding information means more than files - it affects names, faith in service, survival itself. Ideas here cover basics through sharper tools. Each part aims to clarify what shields matter most right now.
Change is moving fast across every kind of company now, opening new paths to grow, save time, move quicker. Still, that shift brings bigger dangers online - attacks evolve constantly, becoming harder to stop. Smaller firms face a tough spot: they rely heavily on tech just to run things but rarely have strong defenses, skilled staff, or deep pockets like big players do.
Not long ago, renting gear wasn’t common. Today, more people and companies choose rentals instead of buying. Owning less means fewer headaches with upkeep or storage. Flexibility matters now - workers move fast, needs change quick. Paying only when you need tech helps budgets stretch further.
Not long ago, renting gear wasn’t common. Today, more people and companies choose rentals instead of buying. Owning less means fewer headaches with upkeep or storage. Flexibility matters now - workers move fast, needs change quick. Paying only when you need tech helps budgets stretch further.
Imagine how fast things move now that everything runs online. Moving work to digital platforms boosts speed and opens fresh options, yet leaves companies open to clever hackers. A single break-in might drain money fast, hurt trust forever, leave private details out in the open.
Connect with Us
Have an IT challenge to solve, interested in joining emdee inc., or just want to reach out? We’d love to hear from you!